The Gist
Trojan Horse malware is becoming the cyber attack of choice popular as hackers are becoming more capable at breaking into networks undetected.
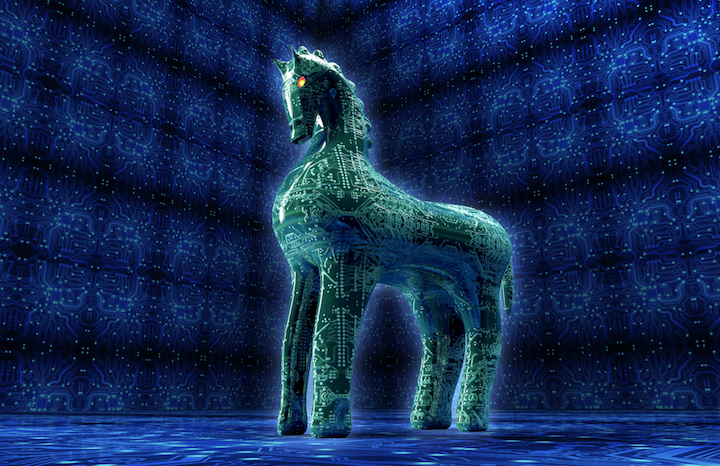
We all know the famous tale of the Trojan Horse. The great city of Troy had walls that protected them from all enemies, until they invited them into their gates unknowingly with the help of a wooden Horse. With something so obvious, there is no way you could ever fall for that…. Or could you?
In the world of cyber attacks, your computer would be the “impenetrable” gates of Troy, and someone’s crafty malware would be the destructive Trojan horse, aptly named the Trojan Virus. With the unique ability to hide itself in the form of legitimate software, downloading this program can infect your computer instantly. Often going undetected, you are unknowingly giving cyber criminals the ability to spy, steal, and gain backend access to all of your private systems.
“With recent examples such as the Carbanak Trojan malware attack, we saw cybercriminals make off with over $1 billion, as evidence of the increasing capability of Trojans to get inside networks undetected. “ – Symantec
Because of the stealthy nature of the Trojan Horse, this malware has become the popular cyber attack of choice by many online hackers. This type of versatile malware can allow cyber criminals to delete data, create backdoor access into your security systems, spy on your personal accounts, steal passwords, and even take full control of your computer with little to no effort.
While being aware is always beneficial, it can’t guarantee your protection. Cyber criminals are only getting smarter as they are figuring out how they can do very little work on their end to create extensive damage on ours. Keep your network safe, and build your wall of protection with powerful network security. With 24/7 monitoring and reporting, Affant will boost your defenses so that you won’t have to face your Trojan Horse.
Resources

Affant Director of Engineering since 2000. Management of engineering and support team, Escalation of all technical and client issues. Sales and design engineer.